The new Multi Factor Authentication (MFA) provides an additional layer of protection around access to your AWS Console and AWS Portal. As you recall from Part 1, controlling access to these areas is vitally important because they in turn allow access to all of your other AWS resources and credentials.
To use MFA, you need to sign up for the service and buy an inexpensive security device such as the one shown below:
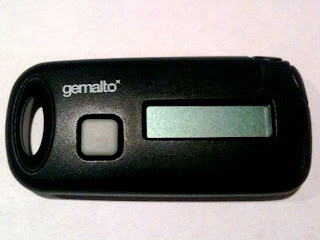
Once you have the device and are registered for MFA, when you attempt to log in to your AWS Portal or AWS Console, you will be asked for the email address associated with the account, the (hopefully very strong) password associated with the account and then finally you will be asked to enter the 6-digit number that appears on your device when you press the little grey button.
That means that even if someone discovers your password, they still need the device before they can log in. And, even if they have the device, they still need your password. Hence the name, Multi-Factor. The devices are inexpensive and the additional security they provide for your AWS credentials is well worth the cost. I highly recommend MFA. At least for your production credentials.
Another useful new security capability is Key Rotation. This is automatically enabled for all AWS accounts and allows you to create a new AccessKeyID and SecretAccessKey but allow the old ones to remain active. In that way, you can create new keys and then begin transitioning your servers to use the new credentials and when the transition is complete, you can then disable the old credentials. That's handy anytime you think you may have been compromised but its also a good idea to do it as part of a regular security routine.
Brilliant. Thank you for pointing out this new security feature. I have been waiting for it.
ReplyDeleteDo you think it is possible to use same device to encrypt ec2 image?
Usual problem - it can only be shipped to US address. Bang.
ReplyDeleteI just ordered from India and they do ship to India, so thats not a problem I suppose.
ReplyDeleteHowever, shipping charges were almost same as the charge of the device :-(